Attempts to gain access to information, such as identity details, login credentials, and payment information, are the most commonly reported cyberattack, with vishing (voice phishing, or phone scams) and email phishing still the most successful means of solicitation, according to the Australian Competition & Consumer Commission’s Scamwatch.
Attackers don’t discriminate by business type or industry, because all businesses share one key vulnerability that can be easily exploited: humans. Phishing messages often use social engineering tactics that provoke a human response, such as empathy, curiosity, fear, or urgency, to increase the likelihood that the recipient will act quickly in the scammer’s favour.
For example, it was common in 2020 for attackers to piggy-back off critical government messages by sending phishing mail that mimicked government communications around COVID-19, tax time, and updates about JobKeeper payments. This capitalised on the increased attention people were paying to such messages at the time, and the heightened anxiety we all harboured during the pandemic.
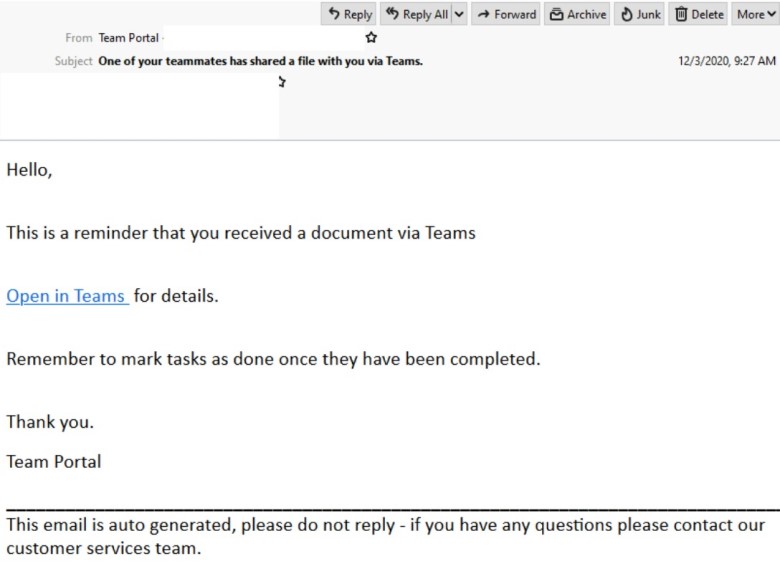
Recently, work-related software has been a ploy for fraudsters, with phishing emails claiming to be from Zoom, Docu-sign, and Microsoft Teams. These type of scams take advantage of the increased instances of staff working from the home office and relying on online collaboration software.
In 2021 we can expect much of the same from scammers, and it's smart for businesses to upskill their staff on all things phishing in order to avoid falling into a phishing trap. Find out more on how to identify hoax messages.
CommBank branding a plot for scammers
As usual, CommBank customers have been on the look-out for phishing scams, reporting suspicious messages to [email protected].
An enduring trend in CommBank brand abuse is phishing and smishing messages that attempt to engage customers with warnings of potential danger, such as alerts about unusual transactions or suspicious activity linked to their accounts.
The lure here is the false sense of urgency to provoke fear and reactivity. Unfortunately, such phishing messages can be well-designed and closely replicate legitimate CommBank communications, so it's crucial to stay vigilant in order to defend yourself or your business against scam activity.
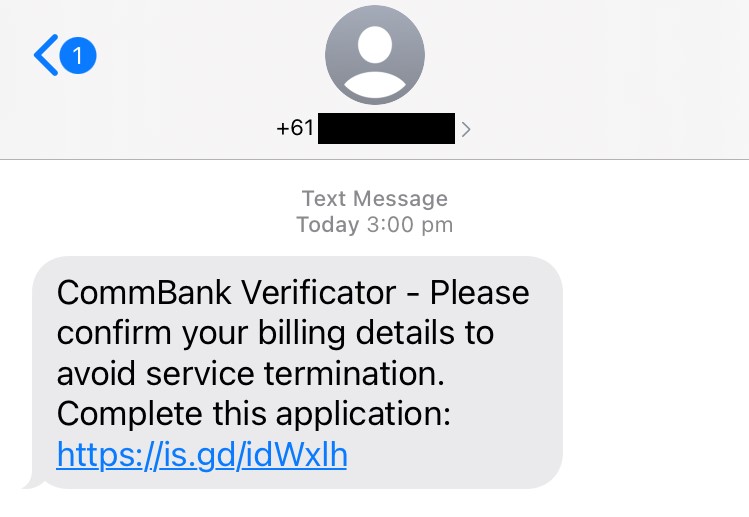
The example below is typical of smishing attempts we see targeting our customers. The recipient is prompted to follow a link to confirm billing details or else suffer ‘service termination’. Links such as this may be designed to steal information, such as login credentials, personal information, or financial information, or to download malicious software onto the device.
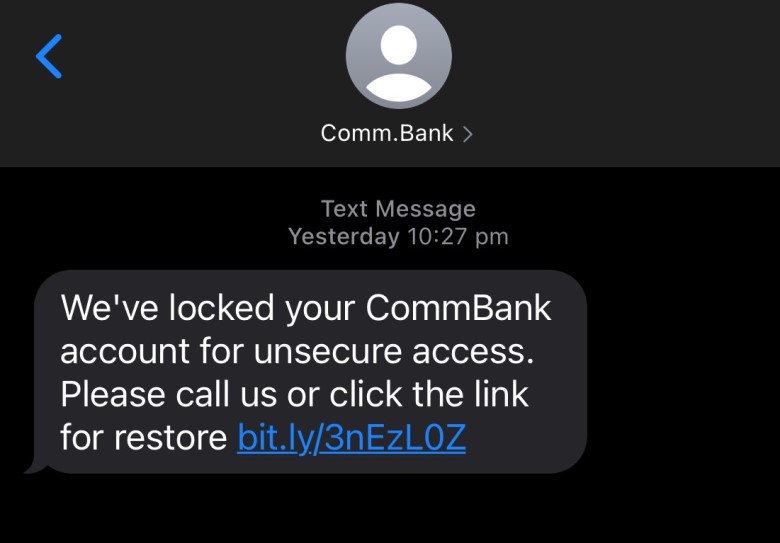
In another smishing example below we can see a similar bid for urgent action, with a fake scenario claiming the recipient’s account has been locked due to ‘unsecure access’, and a claim that clicking the link will restore the account. Notice how the sender name appears as ‘Comm.Bank’.
Spoofing, or imitating, a sender address is a tactic that scammers often use to trick recipients into believing the message is legitimate. Remember that CommBank will never ask you for your banking information by email or text message, and always remain sceptical of any messages that ask you to confirm, update or share personal or banking information.
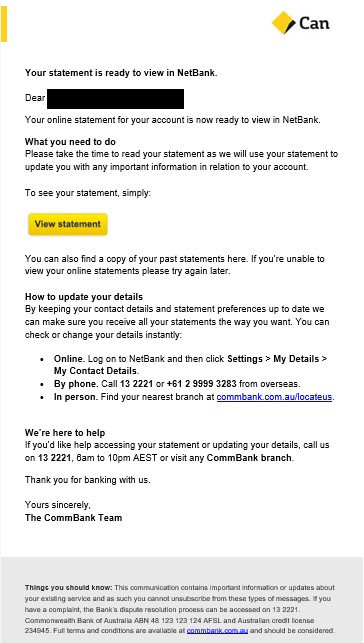
In the final example below, we can see how attackers imitate legitimate CommBank communications. This phish is a dangerous example of how real email notifications can be repurposed by scammers for nefarious activities. In this case, a malicious link has been obscured by the ‘View statement’ button.
The Bank’s Cyber Crime team is yet to see any phishing scams using the new CommBank branding. However, it’s unlikely to be long until scammers catch up and update their lures to reflect brand changes. To be safe, always navigate directly to NetBank yourself and log on from the site you know to be genuine, rather than using any links in communications.
If you believe a suspicious message claiming to be from us is lurking in your inbox, don’t engage with it. Instead, report the suspicious message to [email protected] then immediately delete it.